Lindell v. U.S. Dominion Inc., et al. has 17 exhibits. Exhibits are trial evidence and are subject to objections made by opposing attorneys. These exhibits are provided to support the allegations of wrongdoing made by the plaintiff, Mike Lindell, against the defendant, in this case, Dominion Voting Systems, et al.
See our previous article of Patrick Byrne's announcement of the availability of these documents and Lindell's recent video release Absolutely 9-0.
Exhibit 1: Johns Hopkins University Technical Report on Diebold AccuVote-TS
Exhibit 1 originally appeared as Johns Hopkins University Information Security Institute Technical Report TR-2003-19 in July 2003. It later was published in the Institute for Electrical and Electronics Engineers (IEEE) Symposium on Security and Privacy Computer Society Press in May 2004. It is titled "Analysis of an Electronic Voting System" and is co-authored by Tadayoshi Kohno, Adam Stubblefield, Aviel D. Rubin, and Dan S. Wallach.
It is a security analysis of the source code of the Diebold AccuVote-TS. The authors' abstract reads:
"Our analysis shows that this voting system is far below even the most minimal security standards applicable in other contexts."
It goes on to say several problems are identified, including network vulnerability, incorrect use of cryptography, and inelegant design.
"We show that voters, without any insider privileges, can cast unlimited votes without being detected... that said, we demonstrate that the insider threat is also quite considerable... not only can an insider, such as a poll worker, modify the votes, but [also] violate voter privacy... We conclude that this voting system is unsuitable for use in a general election."
Beyond conclusions for this particular Diebold electronic elections system, the report notes that "Any paperless electronic voting system might suffer similar flaws, despite any 'certification' it could have otherwise received." The technical report suggests a "voter-verifiable audit trail" that would print a physical ballot the voter could verify for a solution to these known vulnerabilities.
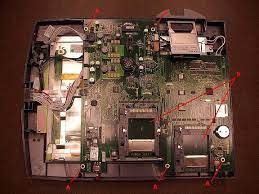 Image Diebold AccuVote Motherboard
Image Diebold AccuVote Motherboard
Diebold acquired a Texas technology company, branded it Diebold Election Systems in 2002, and sold it to Election Systems & Software (ES&S) in 2009. According to a letter from a NH Attorney General's office related to the Windham 2020 voting results, the AccuVote device was "originally manufactured by Unisys, then by Global elections Systems, Inc., which are no longer in business."
The letter also claims that Dominion "owns the intellectual property of the AccuVote and its related elections management system," but that Dominion "does not manufacture the device." The letter also says that the AccuVote devices that have been used in New Hampshire elections for 25+ years are no longer manufactured. Recounts there found the machines to have shorted each Republican candidate on the ballot some 300 votes.
Other studies have reviewed this Diebold AccuVote-TS machine as well.
Exhibit 2: Princeton I.T. and Computer Science Study on Diebold AccuVote
Exhibit 2 is titled "Security Analysis of the Diebold AccuVote-TS Voting Machine" and is coauthored by Ariel J. Feldman, J. Alex Halderman, and Edward W. Felten of the Center for Information Technology Policy (CITP) and Department of Computer Science in conjunction with the Woodrow Wilson School of Public and International Affairs at Princeton University.
 The paper claims itself "fully independent" and is a security study of both hardware and software of the AccuVote, which it says is "the most widely used voting platform in the United States" along with its "newer relative," the AccuVote-TSX. It concludes that "analysis of the machine, in light of real election procedures, shows that it is vulnerable to extremely serious attacks." It says that "an attacker who gets physical access to a machine or its removable memory card for as little as one minute could install malicious code" that could undetectably steal votes and modify "all records, logs, and counters to be consistent with the fraudulent vote count it creates."
The paper claims itself "fully independent" and is a security study of both hardware and software of the AccuVote, which it says is "the most widely used voting platform in the United States" along with its "newer relative," the AccuVote-TSX. It concludes that "analysis of the machine, in light of real election procedures, shows that it is vulnerable to extremely serious attacks." It says that "an attacker who gets physical access to a machine or its removable memory card for as little as one minute could install malicious code" that could undetectably steal votes and modify "all records, logs, and counters to be consistent with the fraudulent vote count it creates."
Further, with equipment configured as studied, "An attacker could also create malicious code that spreads automatically and silently from machine to machine during normal election activities—a voting-machine virus." The researchers say that they created working demonstrations of such attacks in the safety of their lab.
https://www.scribd.com/document/510570993/Lindell-v-Dominion-Smartmatic-Exhibit-2
Exhibit 3: Florida Election' Dominion Machine Test
Exhibit 3 is a March 2012 "Voting System Qualification Test Report" from the Florida Department of State Division of Elections under Secretary of State Ken Detzner.
It is a summary describing the process by which Dominion Voting System hardware and software proposed to be used in Florida elections was evaluated and tested, and subsequently certified. It references audit of software code including OSX firmware Version 1.2.7 and GEMS Software, Release 1.21.6, Version 1. Hardware analysis includes the AccuVote-OS, AccuVote-OSX, AccuVote-TSX, AutoMARK voter Assisted Terminal (VAT), and PCS 900/960/960B.
https://www.scribd.com/document/510570997/Lindell-v-Dominion-Smartmatic-Exhibit-3
It appears as a rigorous protocol for testing the systems, including procedures for testing various pen and oval marking combinations, mock recounts, simulated catastrophic failure, and concluding with test results that say there "were no unexpected outcomes resulting from any of the test activities conducted in the examination of the voting system," while referring specifically to "regressed protective count" and "future date stamp" problems for which tests were run, saying no such problems were encountered.
Exhibit 4: Curling v. Kemp and Appeal in Fulton County, GA
Exhibit 4 is a civil complaint, which is a legal document that initiates a lawsuit and informs the defendant of the claims against them, from Curling v. Kemp et al. This case is a civil suit filed August 4, 2017, in the Superior Court of Fulton County Georgia. Plaintiff is the Coalition for Good Governance, along with several individuals who claim standing for damages by the State of Georgia. Defendants are Secretary of State Brian Kemp acting as Chair of the State Election Board, other members of that Board, and various Fulton County election administrators.
https://www.scribd.com/document/510570999/Lindell-v-Dominion-Smartmatic-Exhibit-4
The Plaintiffs sought injunction prior to the 2018 elections. Still, they were denied in a decision signed September 17, 2018, that said:
"The Plaintiffs did not bring their preliminary injunction motions in a sufficient time span to allow for thoughtful, though expedited, remedial relief... Upon considering the totality of the evidence... the Court finds that the Plaintiffs have not carried their burden of persuasion to establish [the] prerequisites for such extraordinary injunctive relief..."
Court opinion was not, however, entirely favorable to the State Defendants, whom it says:
"...have delayed in grappling with the heightened critical cybersecurity issues of our era," and calls the existing election design of Georgia a "dated, vulnerable voting system that provides no independent paper audit trail." The court further opined that it is "gravely concerned " that Georgia elections officials have "...stood by for far too long, given the mounting tide of evidence of the inadequacy and security risks" of systems and software in Georgia and of "serious vulnerabilities of its voting system... which were raised as early as 2016." The court concluded that "further delay is not tolerable."
The Atlanta Georgia Court's conclusionary remarks continue:
"Advanced persistent threats in this data-driven world and ordinary hacking are unfortunately here to stay. Defendants will fail to address that reality if they demean as paranoia the research-based findings of national cybersecurity engineers and experts in the field of elections."
Plaintiff's request for various injunctions would compel changes to the election process in Georgia aiming to increase election integrity. Now in appeals post-2018 elections, the injunctions would only apply to the 2020 election and beyond. They were granted in part and denied in part by Judge Amy Totenberg, who stated:
"The narrowly tailored relief order directs that the State Defendants provide at least a modicum of the voting backup plan tools essential to protecting voters' constitutionally protected ability and right to cast a ballot that is counted and given the same weight as any other," and further noted, "It is not too late for Defendants to take these reasonable concrete measures to mitigate the real potential harms that would otherwise likely transpire at precinct polling locations," by the 2020 General.
Future articles will further summarize the rest of the exhibits in Mike Lindell v. Dominion / Smartmatic et. al.
Also, see our breakdown of "Exhibit 12" that Patrick Byrne called the "MOAB."


